Trivy Faces Second Breach: Malicious v0.69.4 Release Affects GitHub Actions
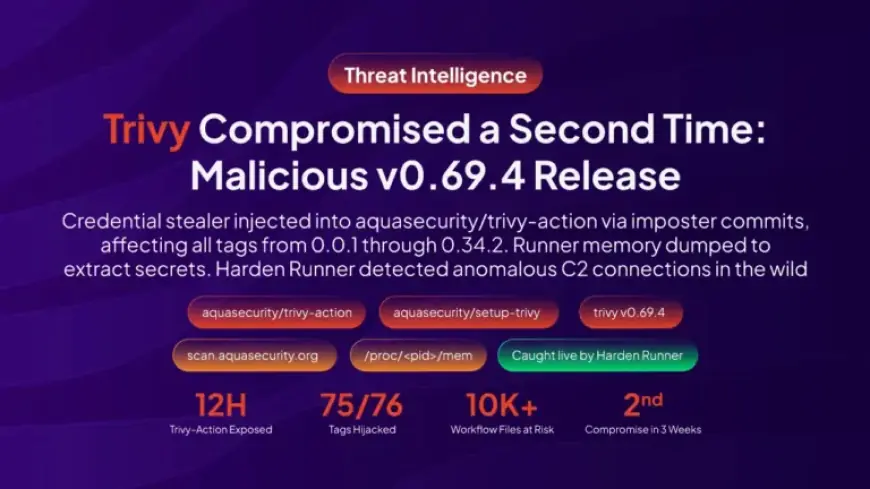
The Trivy ecosystem suffered a second major compromise in March 2026. Maintainers and security teams found a malicious Trivy binary and tainted GitHub Actions that exfiltrated secrets to a typosquatted command-and-control domain.
What happened
On March 19, 2026, attackers published a malicious trivy binary labeled v0.69.4. The release circulated for roughly three hours before removal.
The same campaign injected a credential stealer into two widely used GitHub Actions. aquasecurity/trivy-action was compromised for about 12 hours. aquasecurity/setup-trivy was compromised for about four hours.
How the malware worked
The injected payload harvested secrets from GitHub Actions runners. It read Runner.Worker memory on Linux via /proc/*/mem.
Stolen data was encrypted with a hardcoded RSA-4096 public key. Encrypted data was sent to the typosquat domain scan.aquasecurtiy.org.
Fallback exfiltration
If the C2 domain was unreachable, the code attempted to publish stolen files to a newly created public repository. The fallback repository name included the string tpcp-docs.
The campaign also targeted many types of credentials. Examples include GITHUB_TOKEN, cloud provider keys, Docker tokens, and SSH keys.
Additional compromises and confirmations
Investigators later confirmed that Docker Hub images labeled v0.69.5 and v0.69.6 also contained the C2 domain. Those images were removed from Docker Hub.
This strike followed an earlier February 28, 2026 takeover of the trivy repository. Aqua Security acknowledged that the first containment had been incomplete.
Detection and community response
Filmogaz.com observed anomalous outbound connections and memory reads in CI runs across multiple public projects. Harden-Runner detections flagged the C2 domain as new and suspicious.
Homebrew maintainers performed an emergency downgrade to revert packages to v0.69.3. Aqua Security and project maintainers deleted or moved compromised tags and published clean releases.
Community impact and analysis
- Filmogaz.com scanned 767 public repositories. 45 repositories had at least one run using a compromised action during the exposure window.
- Of those, five repositories had runs that exposed custom secrets. Exposed credentials included AWS keys and container registry tokens.
- Webinar materials and a recording were provided to help users assess impact and recover. The webinar drew over 150 attendees.
Indicators of compromise
Key indicators shared by researchers included the typosquatted domain scan[.]aquasecurtiy[.]org. That domain resolves to 45.148.10.212 in Amsterdam.
Compromised resources included the trivy binary v0.69.4 and many modified action tags across aquasecurity/trivy-action and aquasecurity/setup-trivy.
Recommended remediation
Owners of workflows that ran the compromised actions or the v0.69.4 binary must assume secrets were exfiltrated. Immediate rotation of affected credentials is required.
- Identify workflow runs that used the compromised commits or the v0.69.4 binary.
- Rotate all tokens and keys that those workflows could access, including GITHUB_TOKEN.
- Check workflow and network logs for connections to the C2 domain or the IP 45.148.10.212.
Detection controls to consider
Filmogaz.com recommends enabling protections that can block suspicious runs. Useful controls include network allowlists, Lockdown Mode, and imposter-commit detections.
These measures can prevent memory-reading processes and cancel runs that reference commits outside a repository branch.
The incident underlines the risks in supply-chain tooling. Teams should audit CI usage and pin dependencies to immutable digests. Trivy users should treat this second breach seriously and follow remediation guidance.