FBI Recovers Deleted Signal Messages from Defendant’s iPhone

The recent recovery of deleted Signal messages from a defendant’s iPhone has raised concerns over the security of encrypted messaging applications. Signal, known for its end-to-end encryption (E2EE), allows users to communicate securely by scrambling messages during transit. However, the FBI’s actions demonstrate that no messaging platform is entirely foolproof against external scrutiny.
FBI Recovers Deleted Signal Messages from Defendants’ iPhone
As reported by 404 Media, the FBI successfully extracted incoming Signal messages from an iPhone belonging to a defendant involved in a case related to vandalism and violence at the ICE Prairieland Detention Facility. Notably, the defendant had deleted both the Signal app and its messages, believing that this would safeguard their communications.
How Messages Were Retrieved
Contrary to expectations, the FBI did not need access to the Signal app to recover the messages. They utilized the iPhone’s push notification database to extract received messages, even though these messages were set to disappear within the app. Although outgoing messages were not retrievable, the incoming messages provided vital information.
- The mechanic behind this recovery lies in the way iOS handles notifications.
- If an app is permitted to display previews on the Lock Screen, it saves these alerts in the phone’s internal memory.
Broader Implications for App Security
It’s important to note that this recovery method is not exclusive to Signal. Any app that displays notifications on an iPhone can suffer from similar vulnerabilities. The array of alerts existing in a user’s Notification Center—such as text messages, reminders, and news updates—could be accessed by anyone with the capability to analyze the device.
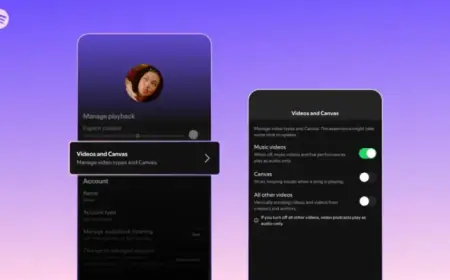
Enhancing Your Security with Signal
For Signal users, there is a proactive approach to enhance privacy. Signal provides an option to hide message content in notifications. This setting can prevent unauthorized viewing of message details.
- To enable this, open Signal and tap on your profile in the top-left corner.
- Select “Settings” and go to “Notification Content.” Choose “No Name or Content” to restrict alerts.
This feature allows users to retain privacy during potential breaches while still keeping track of incoming messages. However, for those who wish to know the sender’s identity, the “Name Only” option can be selected. It’s crucial to weigh the risks associated with viewing sender information against the potential exposure to unwanted access by others.
The FBI’s recent discovery serves as a reminder that while encrypted messaging is a step towards secure communication, it is not an impenetrable solution. Users should always be vigilant and aware of the inherent vulnerabilities present in mobile technology.