FBI Leveraged iPhone Alerts to Recover Deleted Signal Messages

A recent report from 404 Media highlights that the FBI successfully retrieved deleted Signal messages from an iPhone by accessing the device’s notification database. This revelation came to light during a trial related to vandalism activities involving a group at the ICE Prairieland Detention Facility in Alvarado, Texas.
Details of the Case
The trial featured a defendant named Lynette Sharp, who had previously admitted to providing material support to terrorists. During court proceedings, FBI Special Agent Clark Wiethorn discussed the evidence collected from Sharp’s phone.
Recovery of Deleted Signal Messages
It was revealed that the FBI could access incoming Signal message content even after the app had been deleted from the iPhone. According to a summary of Exhibit 158 from a supporter’s website, the content was recovered through Apple’s internal notification storage. Only incoming messages were captured, while outgoing messages remained inaccessible.
- Key Name: Lynette Sharp
- Case Location: ICE Prairieland Detention Facility, Alvarado, Texas
- FBI Agent: Clark Wiethorn
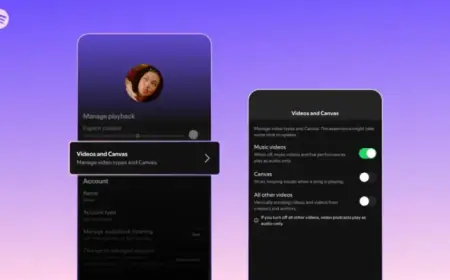
Notification Settings and Data Storage
Signal includes a feature allowing users to prevent the preview of message content in notifications. It appears, however, that Sharp did not activate this setting, enabling the storage of message content in the database. 404 Media attempted to obtain comments from Signal and Apple regarding their notification handling procedures but received no response.
Technical Insights
The specifics regarding the method the FBI employed to recover this information remain unclear. iPhone security is based on various system states, such as:
- BFU (Before First Unlock)
- AFU (After First Unlock)
Each state presents its unique data access limitations. The device’s security measures evolve when it is unlocked, allowing broader access to data. Despite the app being uninstalled, the token for sending push notifications may not be immediately invalidated. Consequently, the iPhone has the discretion to display notifications sent after the app’s removal.
Implications and Future Considerations
Apple recently updated how iOS validates push notification tokens, particularly with iOS 16.4. While the connection to this case cannot be definitively established, the timing raises interesting questions. Additionally, if the FBI retrieved data from a backup, numerous commercial tools are available that exploit vulnerabilities in iOS to facilitate data extraction for law enforcement purposes.
This case underscores the importance of understanding data privacy and the mechanisms that allow for information recovery, even when applications like Signal are deleted.