Researcher Discloses Windows Defender Exploit, Allowing Full Access for Attackers

A security researcher known as Chaotic Eclipse has disclosed a significant zero-day vulnerability in Windows Defender. This exploit, named BlueHammer, enables local users to escalate their privileges to the highest level on a Windows system. The researcher has made the source code available on GitHub, raising concern within the cybersecurity community.
Overview of the BlueHammer Exploit
BlueHammer is a local privilege escalation (LPE) exploit that grants low-privileged users access to the NT AUTHORITYSYSTEM level. This vulnerability allows attackers to execute commands with system-level privileges, putting user data at risk.
Details of the Exploit
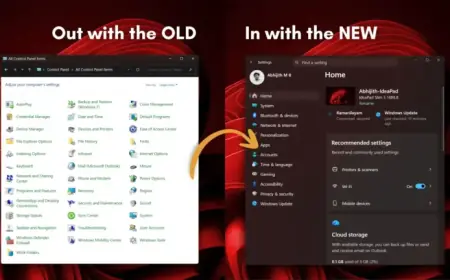
- The exploit operates on Windows 11, specifically Build 10.0.26200.8037.
- A detailed analysis shows Windows Defender being targeted to achieve privilege escalation.
- An operational demonstration highlights that a command prompt from a limited user account can reach full SYSTEM access quickly.
In the demonstration, commands confirmed SYSTEM access and displayed NTLM password hashes for local accounts. This includes data for administrative users, indicating serious security implications.
Motivation Behind the Disclosure
Chaotic Eclipse cited frustrations with Microsoft’s Security Response Center (MSRC) as a primary reason for the public disclosure. The researcher criticized the declining quality of MSRC’s response to vulnerability reports, noting that experienced personnel have been replaced by less knowledgeable staff. This situation has reportedly resulted in delayed resolutions and demanding requirements, like submitting a video demonstration of exploits.
Implications for Cybersecurity
This type of uncoordinated disclosure is becoming more frequent. Researchers often resort to public releases when they feel their issues are ignored. While this action pressures vendors to respond, it simultaneously increases risks for users before a patch is available.
Mitigation Strategies
Until Microsoft releases an official patch, security teams are advised to implement the following precautions:
- Monitor endpoint detection and response (EDR) tools for unusual privilege escalation activity.
- Limit local user permissions to necessary operational levels.
- Enhance logging on Windows systems to identify abnormal SYSTEM-level processes.
- Watch for Microsoft Security Updates addressing the BlueHammer vulnerability.
As of now, Microsoft has not issued a public statement or security advisory regarding this critical vulnerability. Organizations are urged to follow updates closely and remain vigilant against potential exploit attempts related to BlueHammer.
For further cybersecurity news and updates, visit Filmogaz.com.