Xbox Mobile Text Message Braze Alerts Flood Phones — How Xbox Mobile Users Were Affected and How to Reset Notifications
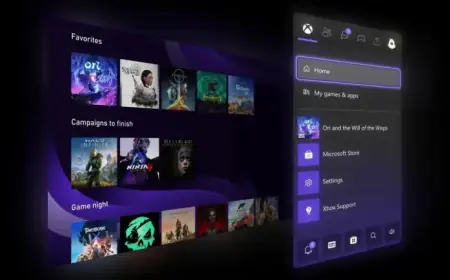
The burst of push notifications that landed on many phones today has a clear immediate victim: Xbox mobile app users who were hit with a rapid sequence of identical alerts that looked like internal test traffic. The lowercase tag xbox mobile text message braze appeared in message copy that referenced a “dummy” alert and prompted users to take a screenshot, fueling confusion and frustration while the company worked to stop the noise.
Who felt the impact and what users reported
Reports poured in from users who received a rapid sequence of identical alerts on their phones the Xbox app, prompting confusion, frustration, and rapid speculation across social platforms. The messages referenced a “dummy” message and named Braze, and they suggested the alert would navigate to a “recently added” view when tapped—classic cues that this was a quality assurance exercise never meant for the public. Users largely described the incident as an annoyance rather than a functional outage, and some opted to silence notifications until the noise subsided.
Xbox Mobile Text Message Braze: the company response and tooling referenced
The platform acknowledged the glitch and said it originated from a test notification that escaped guardrails, adding that service is now back to normal and apologizing for the spam. There is no indication of compromised accounts or targeted malicious activity. Braze is named in the copy; Braze is an enterprise platform used to orchestrate push notifications, in-app messages, emails, and SMS, and its mention signals which tooling was involved rather than a separate app on a device.
How test traffic can reach broad audiences
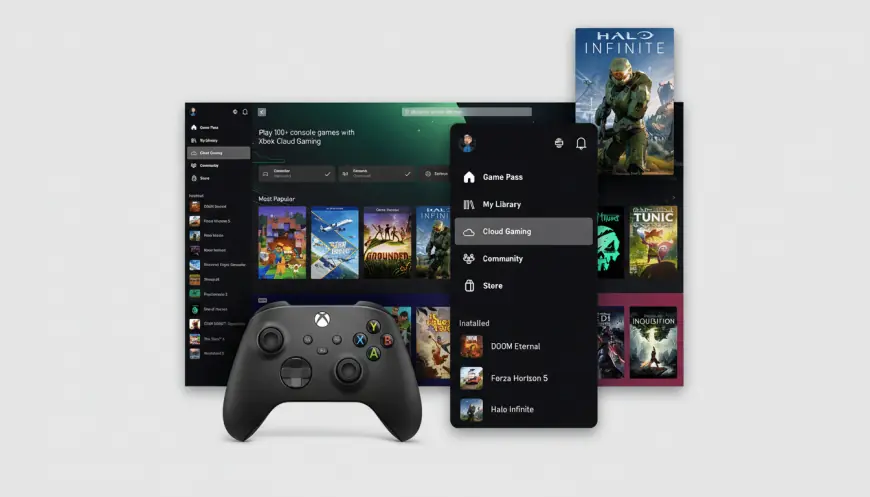
Test messages are typically restricted to internal audiences—often labeled “staff, ” “QA, ” or “staging”—and gated by approvals or environment keys. In practice, test flows are supposed to live in sandbox environments or be sent only to whitelisted employee devices. When those controls slip—through a misconfigured audience segment, an API key mix-up, or a mistaken production toggle—a test can hit the full subscriber base within seconds. Push delivery rides over Apple Push Notification service (APNs) and Google’s Firebase Cloud Messaging (FCM), both designed for speed and scale; if a campaign is queued with a broad audience and no throttle, millions of devices can be pinged almost instantly. Multiply that by retries, multiple variants, or a workflow loop—and you get a cascade of identical pings.
What's easy to miss is that seeing “Braze” in the copy simply signals which vendor handled the message, not a separate piece of software installed on a phone.
Practical fixes and safety checks for affected users
Here’s the part that matters: nothing in the incident suggests a breach. The content was generic, there were no phishing links, and the behavior aligns with an internal QA send gone public. If you were affected, you can safely re-enable notifications after the storm passes. As a precaution, review your Microsoft account’s recent activity and confirm you recognize all sign-ins. If the Xbox app keeps resurfacing old alerts, force-quit and relaunch it, or toggle notification permissions off and back on. Clearing the app’s notification history can also help restore normal behavior.
- Test traffic named “dummy” and referencing Braze reached public users the Xbox app.
- Xbox characterized the flood as overzealous test notifications, said the issue was resolved, and apologized for the spam.
- There is no indication of compromised accounts or targeted malicious activity.
- Common failure modes include misconfigured audience segments, API key mix-ups, or production toggles left active.
- APNs and FCM can deliver a campaign to millions of devices very quickly when not throttled.
How this fits a broader pattern and what to watch for next
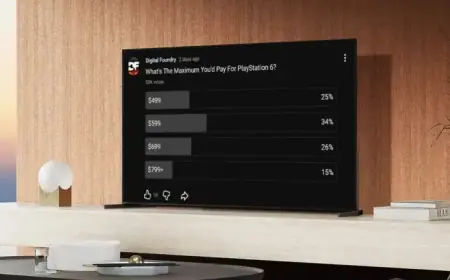
They’re uncommon but memorable: users may recall a global “1” ping from a major smartphone maker’s device locator app or an “Integration Test Email” sent at scale by a prominent streaming service. These incidents tend to be configuration errors, not security events. Customer engagement vendors publish reliability figures in the high-9s, and independent benchmarks from firms like Airship and OneSignal show gaming apps often maintain strong push opt-in rates—frequently above 60% on Android and lower on iOS—which means unclear in the provided context.
The real question now is whether internal safeguards around test audiences and environment keys get tightened to prevent repeat noise. If you’re wondering why this keeps coming up, the combination of powerful delivery systems (APNs/FCM) and human-facing configuration controls is the usual culprit.
(End of coverage drawn solely from the provided context. )