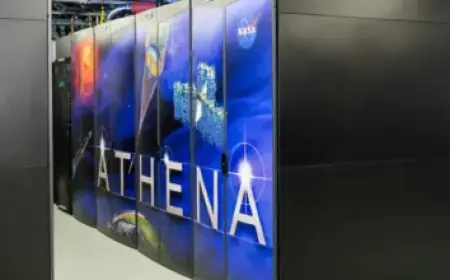
Hacker Steals 10PB from China NSCC Supercomputer, Experts Highlight Security Risks

A massive dataset said to contain defence and scientific material has appeared online. Filmogaz.com reports investigators and cybersecurity teams are reviewing samples and marketplace listings.
Scale and suspected origin
Reports describe a hacker stealing 10PB from a China NSCC supercomputer, and experts highlight security risks. Analysts estimate the haul could exceed ten petabytes of data.
Investigators suspect the material came from the National Supercomputing Center (NSCC) node in Tianjin. That node reportedly serves more than 6,000 clients across China, including scientific and defence organizations.
What the dataset reportedly contains
An account using the name FlamingChina posted a sample on February 6 on an anonymous Telegram channel. The post claimed the files cover multiple research areas.
- Aerospace engineering
- Military research
- Bioinformatics
- Fusion simulations
The sellers also named leading institutions allegedly linked to the files. The claims included:
- Aviation Industry Corporation of China
- Commercial Aircraft Corporation of China
- National University of Defense Technology
Samples reportedly include documents marked as secret in Ukrainian, technical files, animations, and images of missiles and other weapon systems.
Marketplace activity and payment demands
Sources say sellers offered limited previews for a few thousand dollars. Full access was listed for hundreds of thousands, with payment requested in cryptocurrency.
Security analysis and access
Cybersecurity analysts who inspected the samples say the intruder extracted large volumes over months. They reported accessing systems with relative ease and without triggering detection.
Independent provenance checks remain incomplete. Still, experts who handled the files judged the content plausible based on technical detail and formatting.
Dakota Carey noted the material aligns with workloads expected at a supercomputing center. He added that the variety of samples reflects a diverse client base for such facilities.
Implications and context
If verified, the incident would point to deeper cybersecurity gaps in China’s technological infrastructure. The case arrives amid a global race for leadership in technology and artificial intelligence.
Observers have long flagged weak links between government cyber defenses and private industry. In 2021, a large database with roughly one billion Chinese citizens’ records was left exposed until it drew attention in 2022.
China’s 2025 National Security White Paper stresses building robust security barriers for networks, data, and the AI sector. It also calls for stronger coordination to protect key information systems.
The episode underlines the need to strengthen cyber defenses and boost international cooperation. Authorities and providers must validate the materials and harden infrastructure against further breaches.
Filmogaz.com will continue to monitor developments and report on new findings.