Google Faces Bigger Issues Than Sideloading in Combating Android Scams
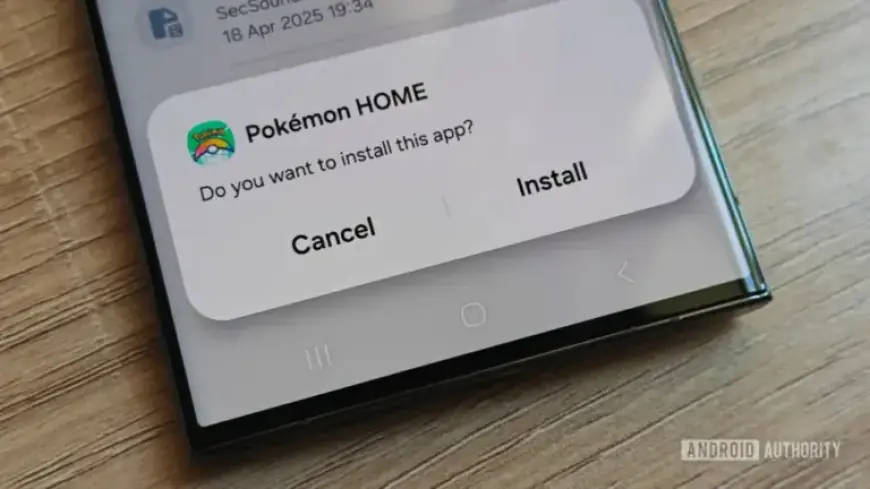
Google has introduced a new sideloading flow that adds several steps to installing apps from outside the Play Store. The change goes into effect in August and aims to block scams that pressure users to install malicious apps.
What the new process requires
The new flow forces users to enable Developer Mode. They must confirm they are not being coached and then restart their phones.
After the restart, a 24-hour security delay begins. Users then may enable the settings that allow sideloading. This 24-hour wait applies once per device.
Critics say the change targets a narrow threat
The flow focuses on coerced installs tied to fake emergencies. Those scams typically rely on social engineering and direct contact with victims.
Those critics argue existing warnings already slow many such attacks. They say the bigger problem is malicious apps on the Play Store.
Play Store malware remains a major issue
Independent researchers continue to find large numbers of malicious apps on Google Play. Zscaler reported 239 malicious Android applications with 42 million downloads between June 2024 and May 2025.
In 2025, the Satori Threat Intelligence and Research Team found 224 malicious apps that accumulated over 38 million downloads. Many of these apps carried out ad fraud.
How malicious apps reach users
Some apps download additional malicious code after users install them from Play listings. Ads can funnel users directly to Play Store pages.
Ads sometimes auto-open the Play Store or hide dismiss controls. That behavior increases the chance a user installs a malicious app.
Trust, permissions, and data safety
The Play Store’s data safety section depends on developer disclosures. That reliance can leave users with incomplete information.
Installed apps may request sensitive app permissions without further Play Store warnings. For example, apps can ask to display over other apps.
Impact on developers and users
Open-source developers who avoid registering with Google say the new flow makes distribution harder. The change may deter legitimate sideloading for valid use cases.
Some users report encountering malware only through Play Store downloads. Personal examples include apps that mined cryptocurrency or requested dubious permissions.
Public reaction and perspective
In a public poll of 157 respondents, 13% believed the new sideloading flow would cut scams. The remaining 87% said it would not, unless Play Store issues are fixed.
Megan Ellis at Filmogaz.com notes the policy increases friction while many Play Store threats remain unaddressed.
What needs to change
Experts suggest stronger Play Store vetting and better ad controls. Improved malware detection could limit millions of risky downloads.
Until those measures arrive, sideloading friction may only treat a symptom. The larger challenge continues to be Play Store malware and Android scams.